Every form of life has become completely extinct in different historical periods. From the extinction of dinosaurs to the glaciations and the disappearance of our fellow human ancestors. The emergence of a new link in the species chain, which has improved physically and neuronally, implies the later disappearance of the predecessor: there are no Neanderthals that have survived the appearance of the Homo habilis.
This approach raises the question: will it be our own hands that lead to our extinction?

During the last decade, we have witnessed technology grow at a constant rate, consistent with our own evolution. However, nothing prepared us as a society to the rapid and unstoppable technological growth that started with the COVID-19 pandemic. The emergence of this global challenge not only meant a public health issue, but also the social isolation of people. It became clear that there was a need to evolve, just like our cave-dwelling ancestors, to stay connected and resilient in this new way of life.
We managed to evolve, technologically, up to ten years in just a couple of them. We realized the infinite possibilities available for us to connect without even leaving our homes. But what happens to our security under these communication channels? In most areas of our daily life, digitalization represents technological evolution by completely changing the rules on how we handle data privacy.
As a new link in the evolutionary chain, artificial intelligence (AI) allows machines to efficiently solve problems or tasks, even better than a human being. In its simplest form, it uses data sets to determine solutions, patterns, and even create them from scratch.
There is an inherent risk in the use of computer systems. We must guarantee that our information is managed securely, regardless of the digital service or system we are using. With the emergence of advanced AI, business approaches to digital platforms are also changing. Should we ask ourselves, then, how the Internet is financed?
Clarissa Véliz Perales, Philosophy and Ethics professor at Oxford University, warned that “the company’s business model is to sell its users’ personal data to banks, insurance companies, governments and other companies that, in turn, resell it and can be used for almost anything […]”, a situation under which most social networks and websites based on AI work. Therefore, it is safe to say that day by day, every second, huge amounts of data are collected, with and without our consent.
Considering the amount of information in cyberspace and technological evolution we are facing, what would happen if all the data that today is encrypted on the network is suddenly opened? If all the private and confidential information in world were to be exposed in a computer with endless capabilities. These computers are called quantum computers, with the ability to analyze and decrypt data in a matter of seconds, with billions of possibilities and meanings.
By employing computers with exceptional physical capabilities and systems based on significantly advanced AI, we could solve almost any problem of humanity… or decrypt data that would cause irreparable damage to society.
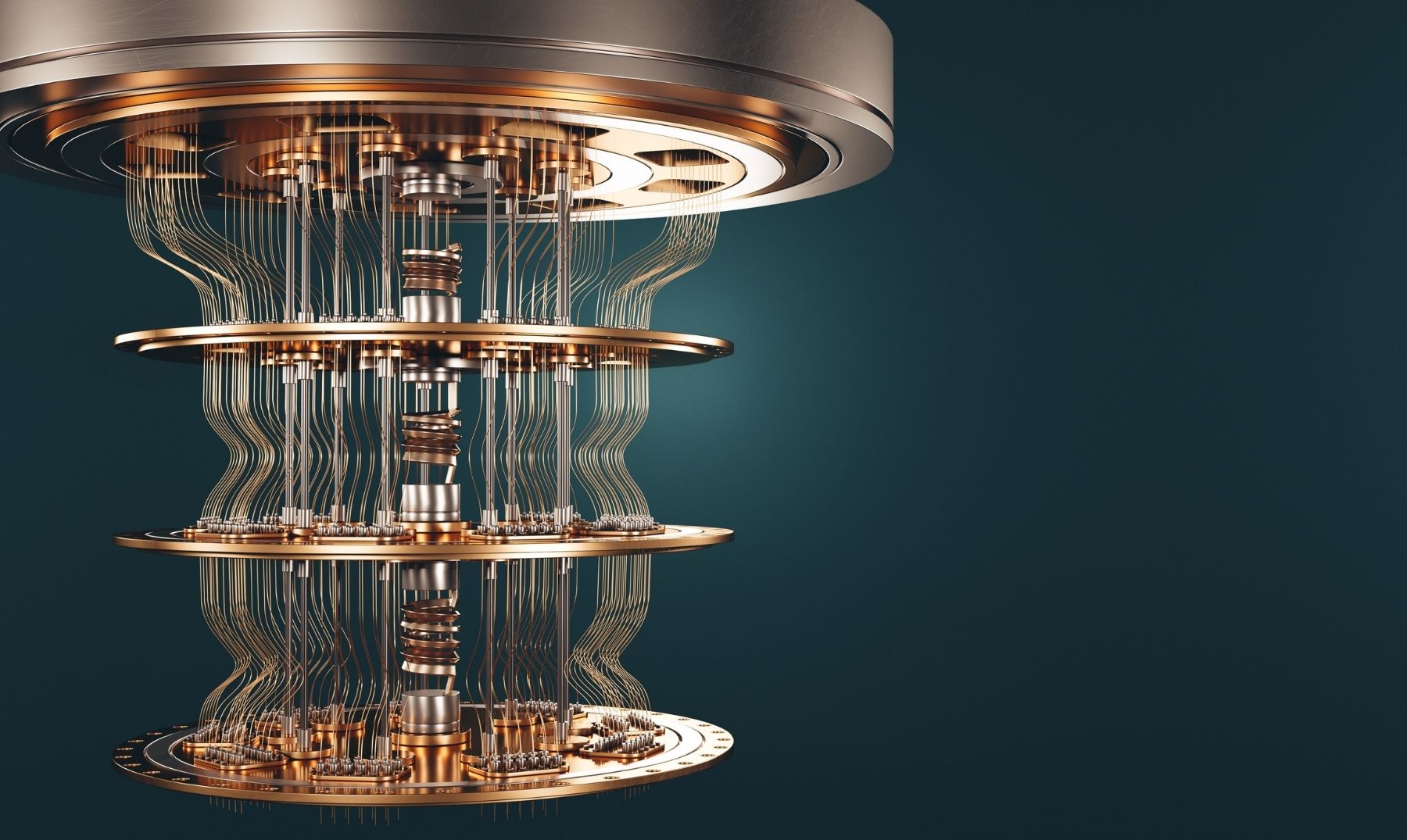
Ilyas Khan, CEO of Quantinuum, explains that quantum evolution is a threat to our lives, stating that “quantum computers will render most existing encryption methods useless.”
When this happens, we will be facing the possible extinction of online privacy and security: the quantum apocalypse.
Unlike apocalyptic prophecies where the Earth is hit by earthquakes and massive floods, the quantum apocalypse will be brought by computers capable of breaking data encryption protocols and schemes. They will create the possibility for those who use them to manipulate information at their convenience. If cybercriminals had access, they could empty bank accounts, block the defense systems of entire governments and access everything considered “private” in the digital world.
Is it time to burn our devices and close all our digital accounts? Is it time for total panic?
The answer is no. Like every point in human history since the first hominid appeared on Earth, evolution cannot be slowed down. Our society, now digitized, cannot turn back the clock on the technological growth on which not only we are dependent for communication, but also to meet our basic needs such as the healthcare sector and food supply chains.
What can I do to protect myself while computing evolves?
Waiting for the evolution to continue may seem too passive an action for Internet users. Currently, we are totally exposed; the culture of personal data protection is still in its early stages, especially in the framework of domestic regulations, so many of the preventive and protective actions need to start at our homes:
- Verify to whom we provide our information: be certain that we provide our data to reliable and truthful entities.
- Block unnecessary requests: as users, we must provide only the necessary data to be able to use digital services.
- Read, read, read: every entity that uses personal data is required by national law to provide a privacy notice or a data processing notice. It is our obligation as users of digital services to read such policies to make sure how and what is done with our data.
Secure passwords: it is essential not to use the same password between low-risk systems and critical systems; for example, do not use the password of a social network in a bank account.
Research has been conducted to generate technological solutions that prevent the quantum apocalypse, establishing cybersecurity strategies to protect all sectors of society, from governments to every individual user with a computer at home. These solutions are called “post-quantum” because they are intended to be computer and quantum intelligence proof. While the changes represent a challenge for any generation, not doing something about it is not an option.