“Visibility into endpoint devices is crucial for understanding and enhancing an organization's overall security posture, regardless of the protective measures in place. Effective collaboration between IT and security teams is key to operational rigor, and tools that provide shared insights, like Metabase Q's Batuta, can significantly elevate a company's ability to proactively manage cybersecurity risks.”
TRUSTED BY LEADERS AND INNOVATORS
OUR SOLUTION
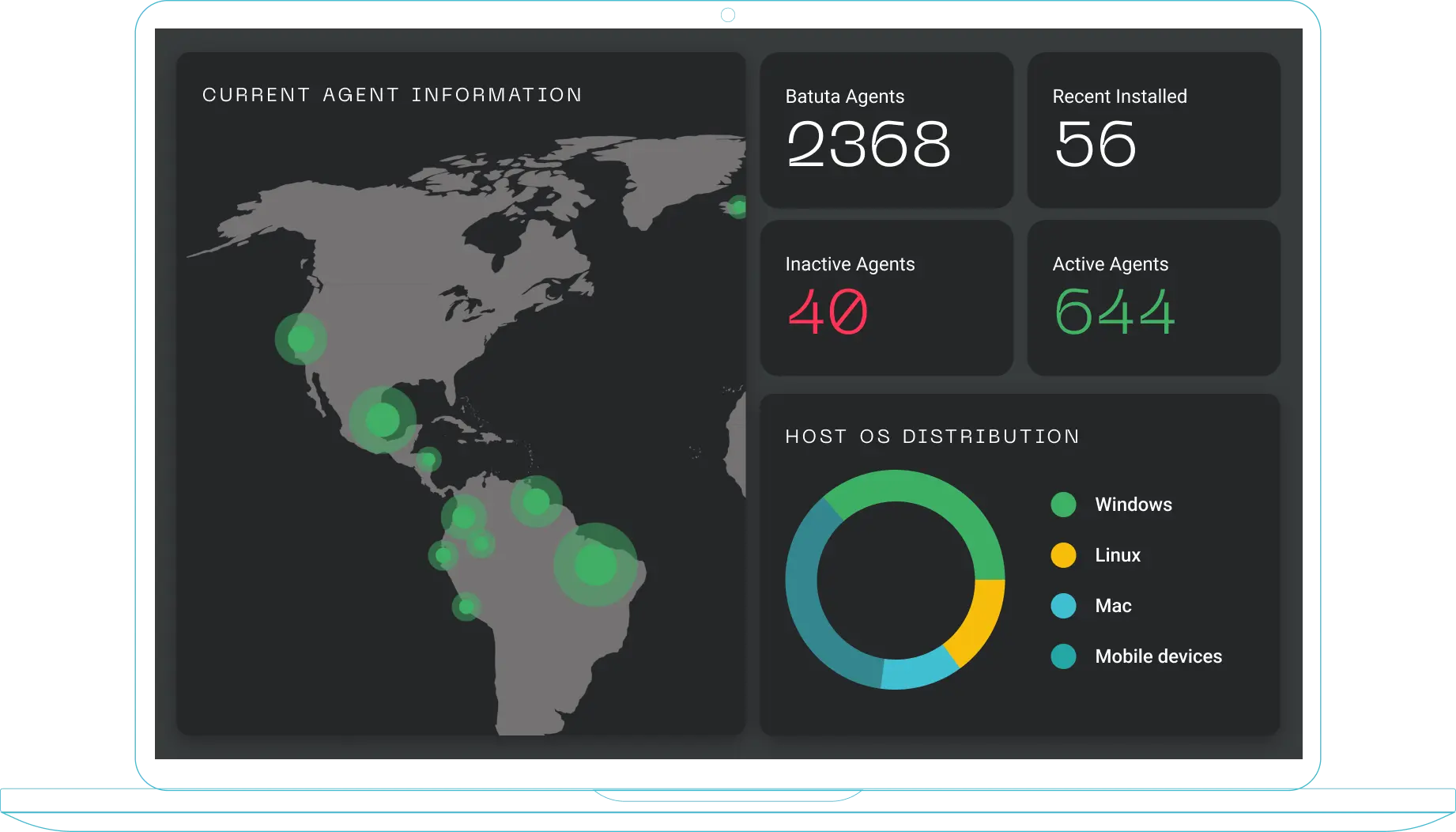
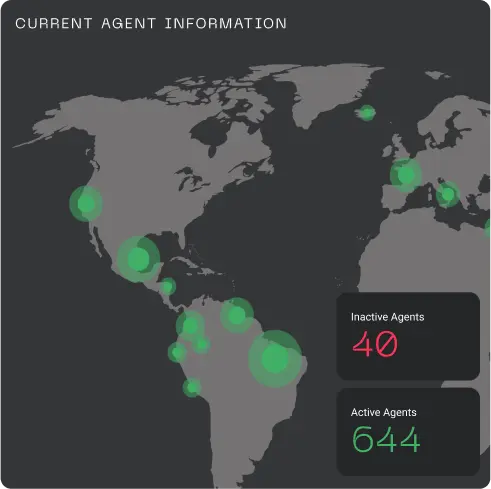
Batuta is a cloud-native, multi-tenant endpoint management platform
We combine IT and cybersecurity functionalities to proactively strengthen companies' security posture
The Batuta Modules
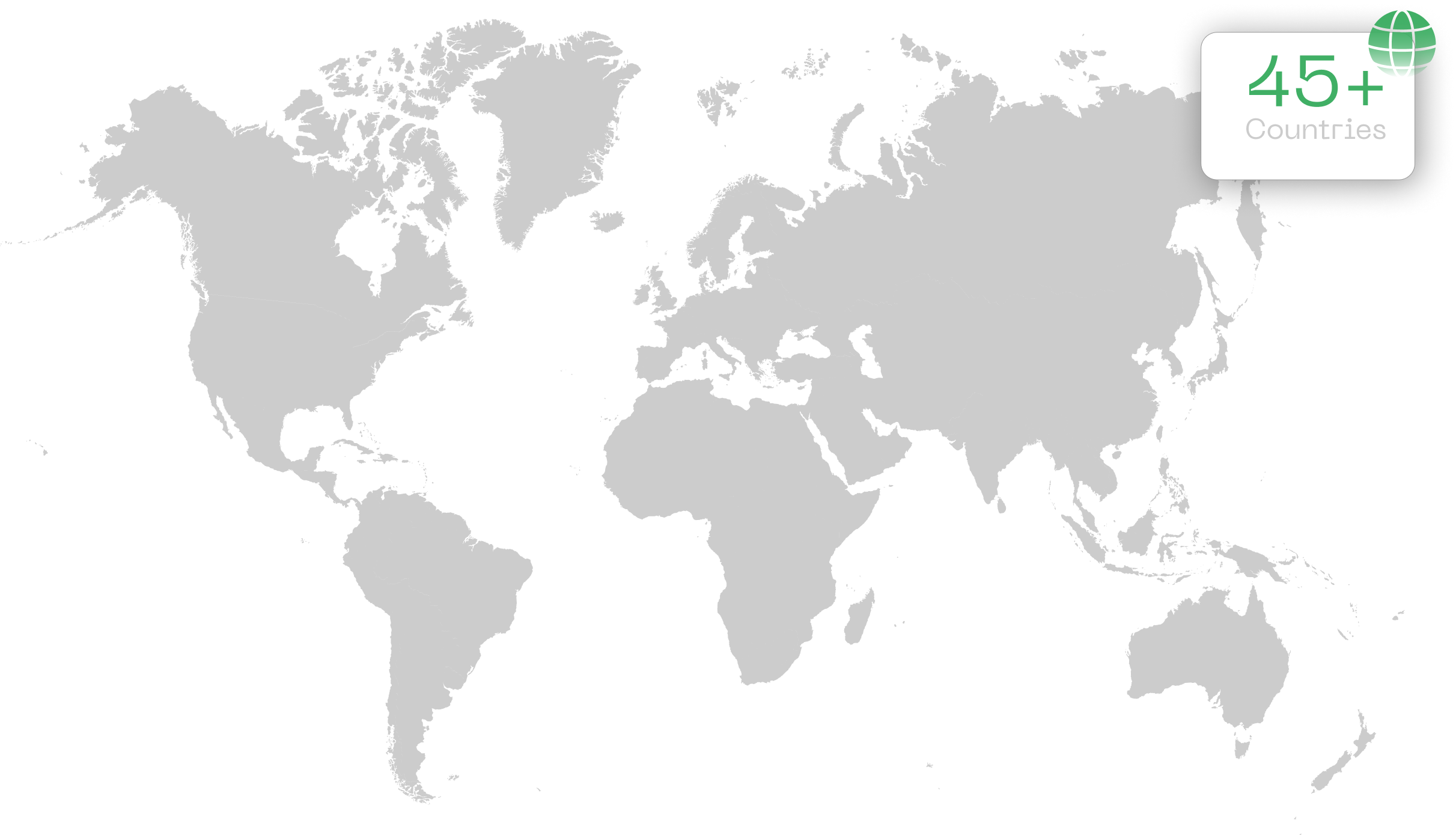
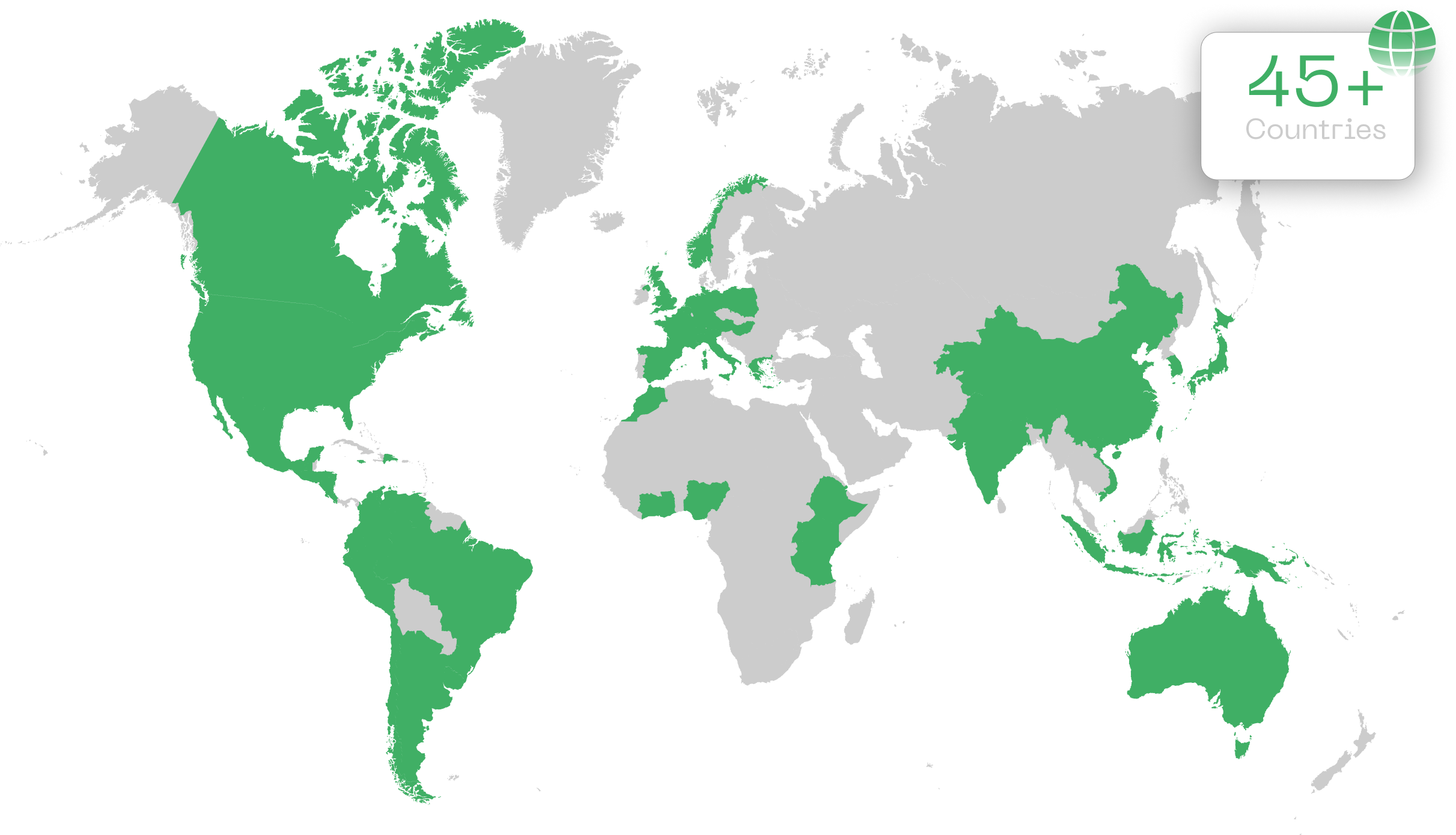
See how we've helped simplify processes, optimize systems and transform businesses and cybersecurity programs around the world
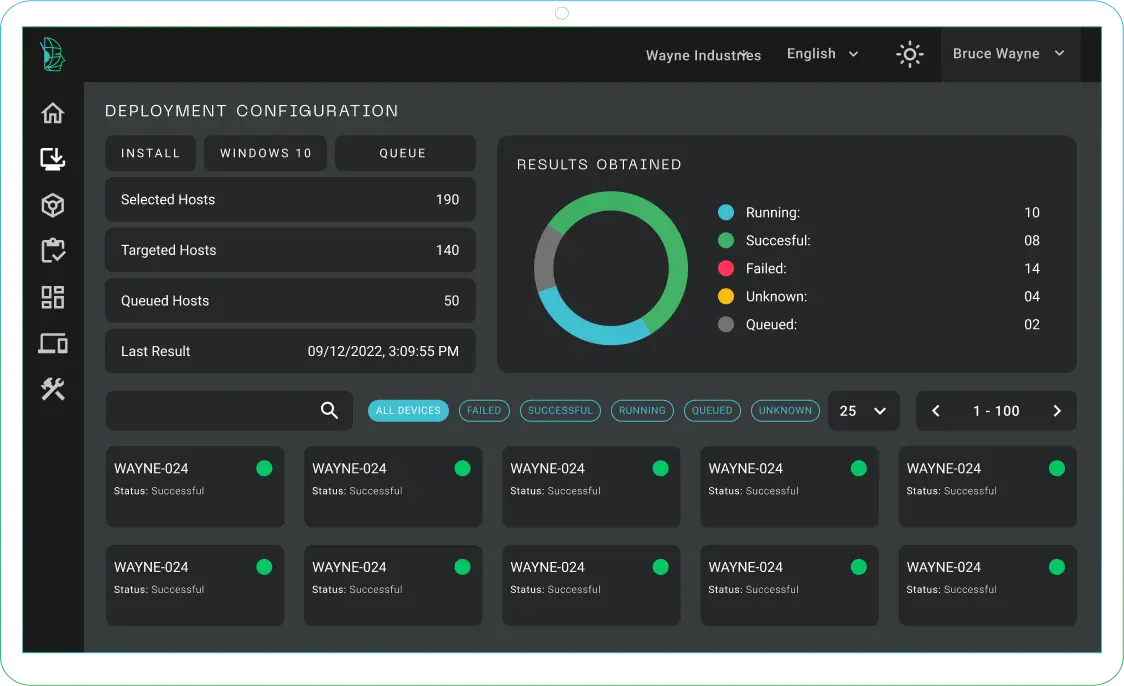
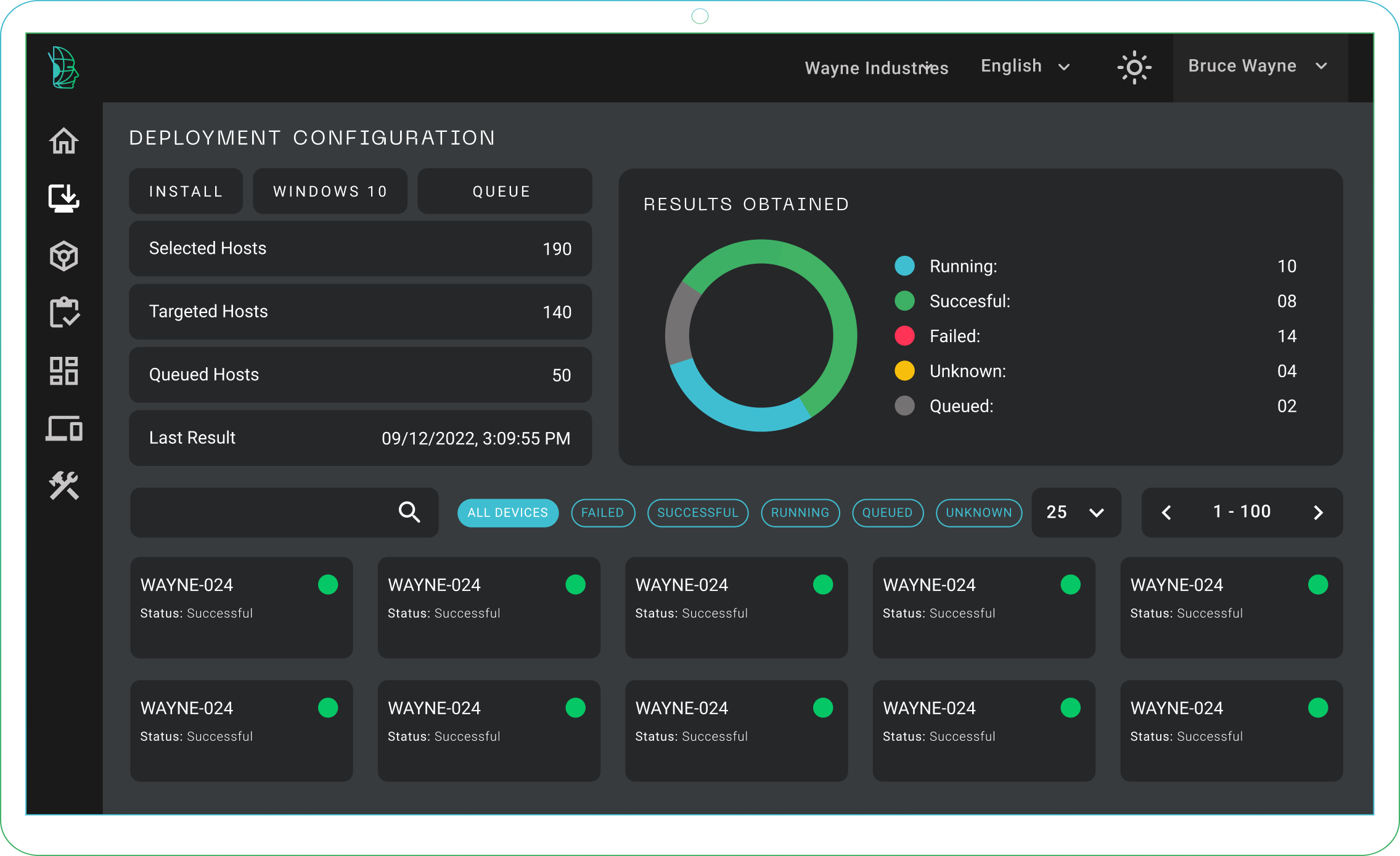
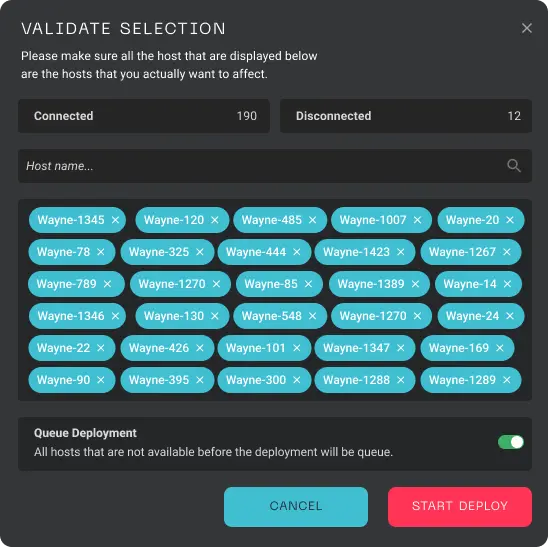
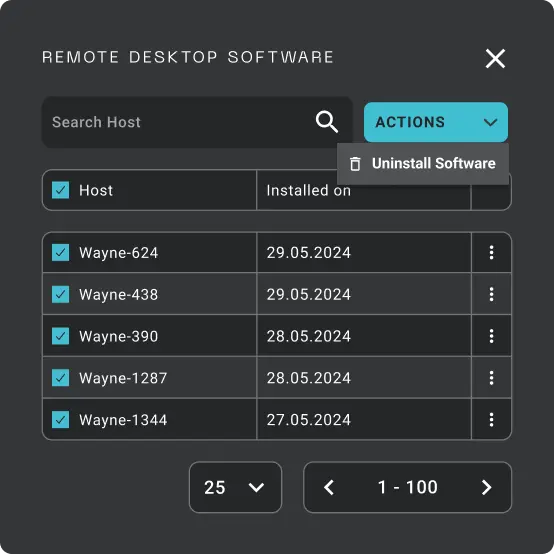
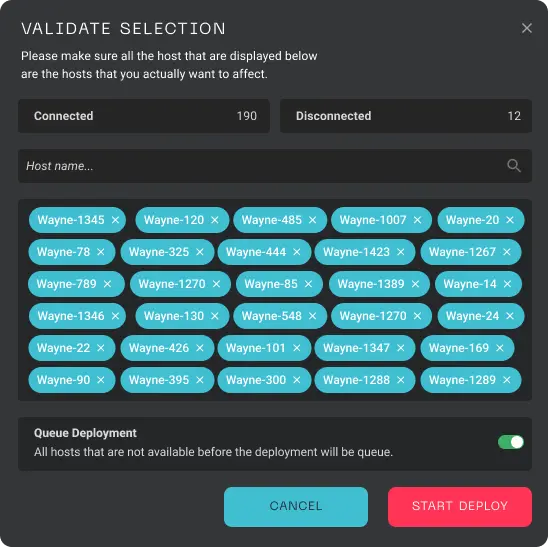
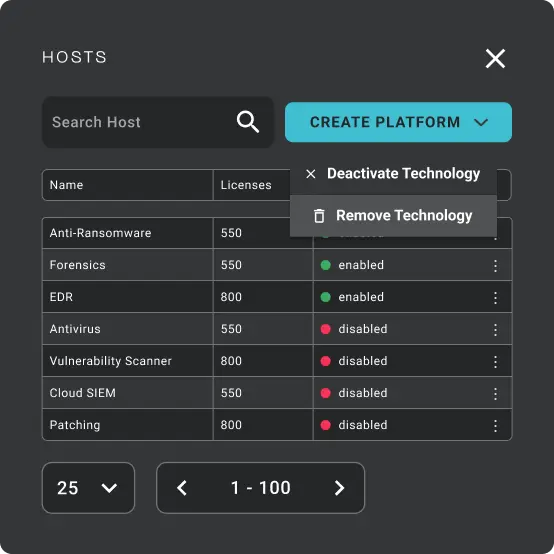
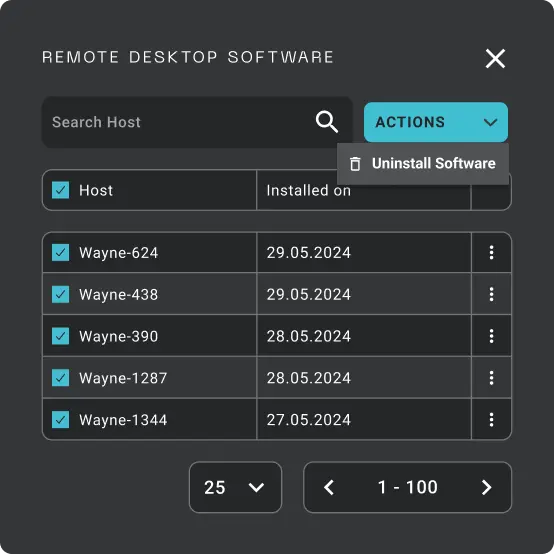
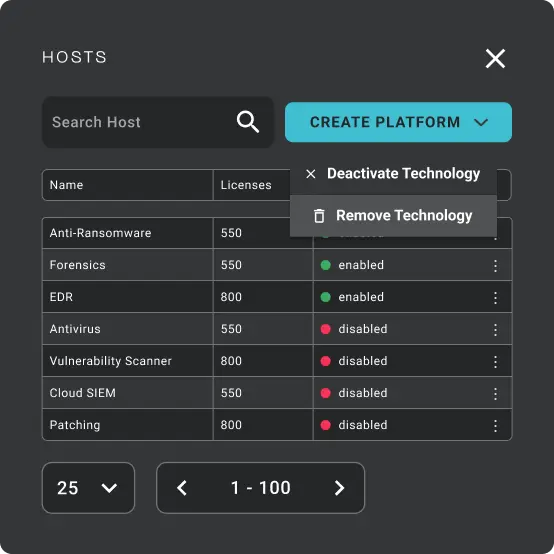
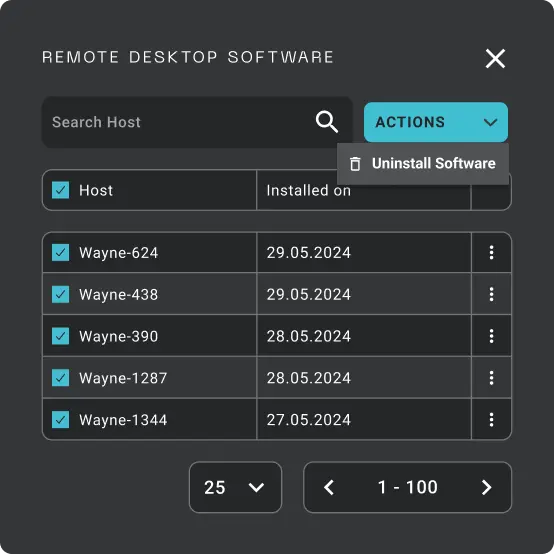
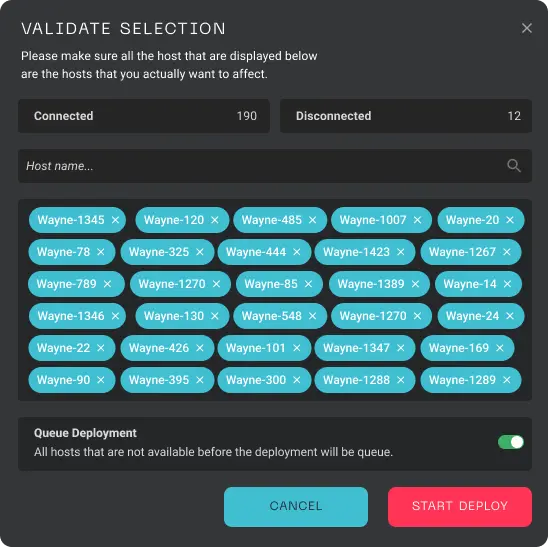
Deploy
Fast-Track your cyber defense operations
- Swift installations for accelerated cybersecurity operations
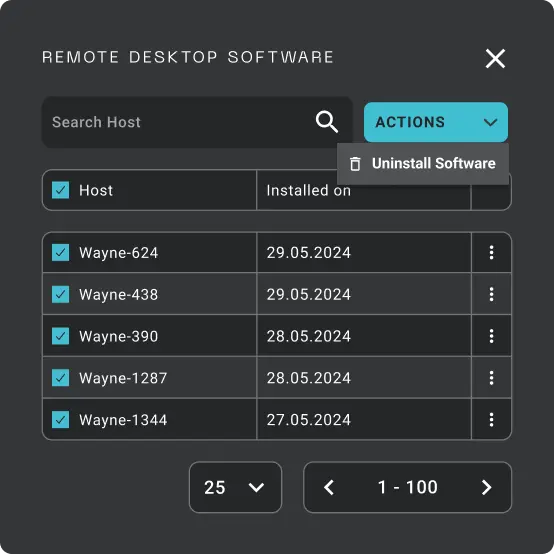
- Intuitive uninstallation process for effortless system maintenance
- Real-time status checks for reliable implementation
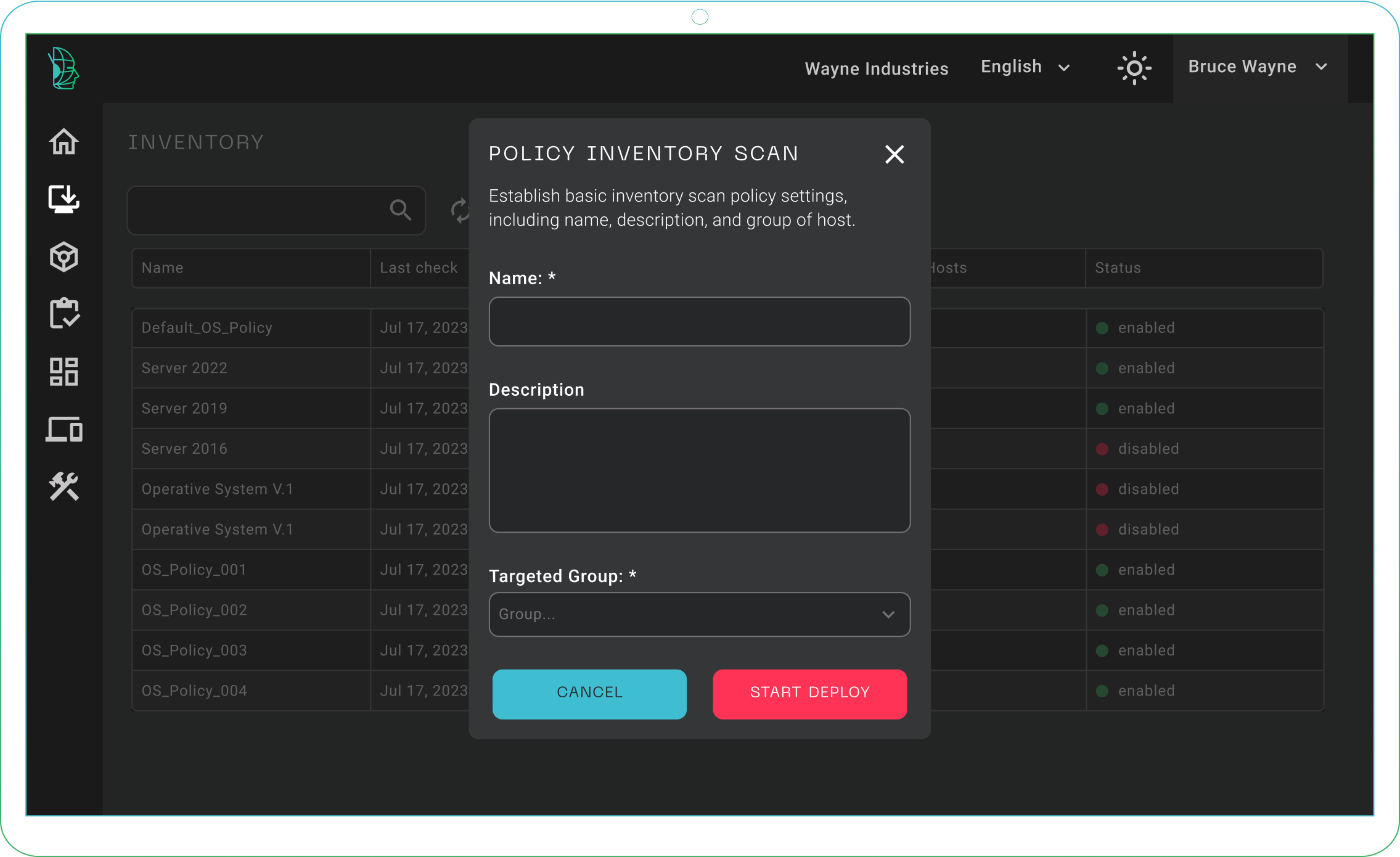
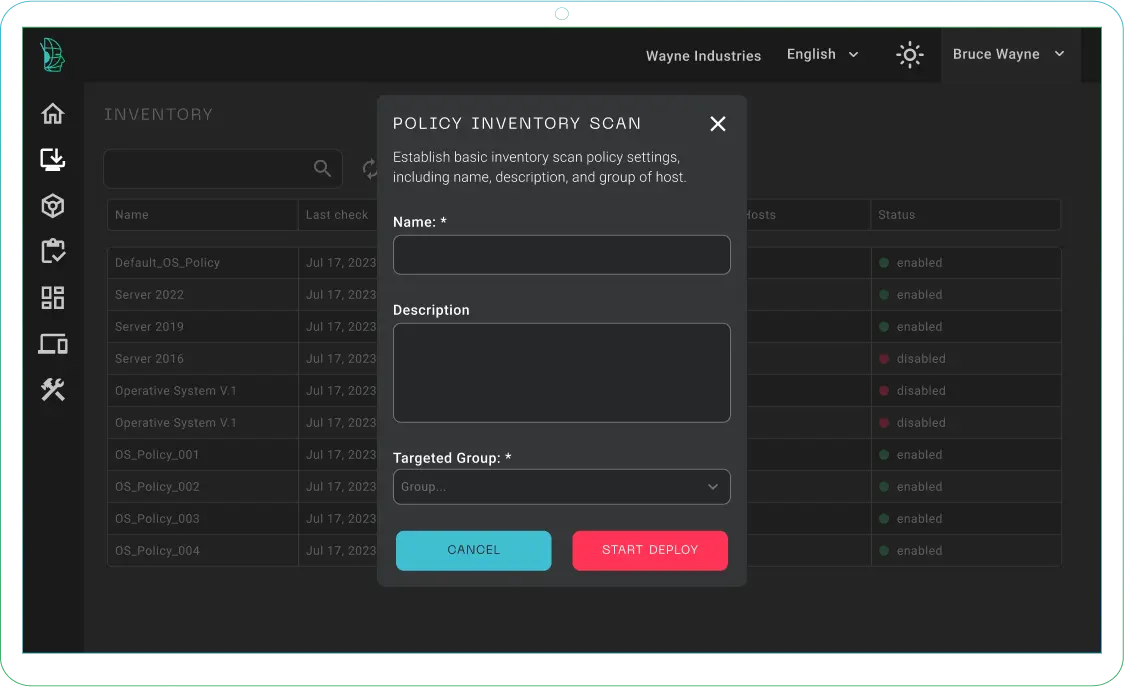
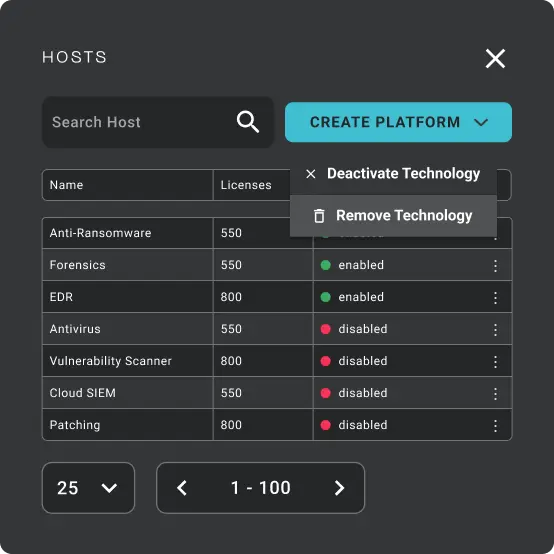
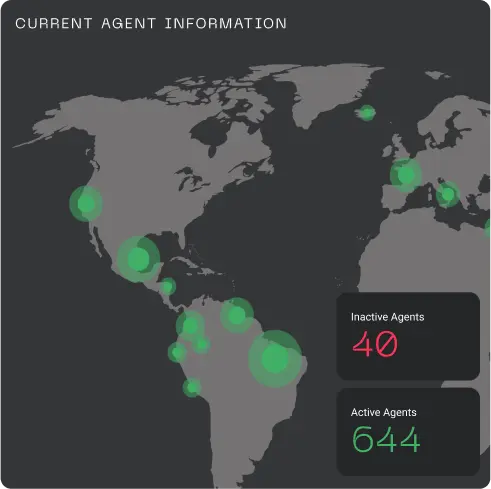
Inventory
Know what you have
- Comprehensive hardware and software inventory for full visibility.
- Efficient asset tracking and management for organized operations.
- Powerful insights for informed decision-making.
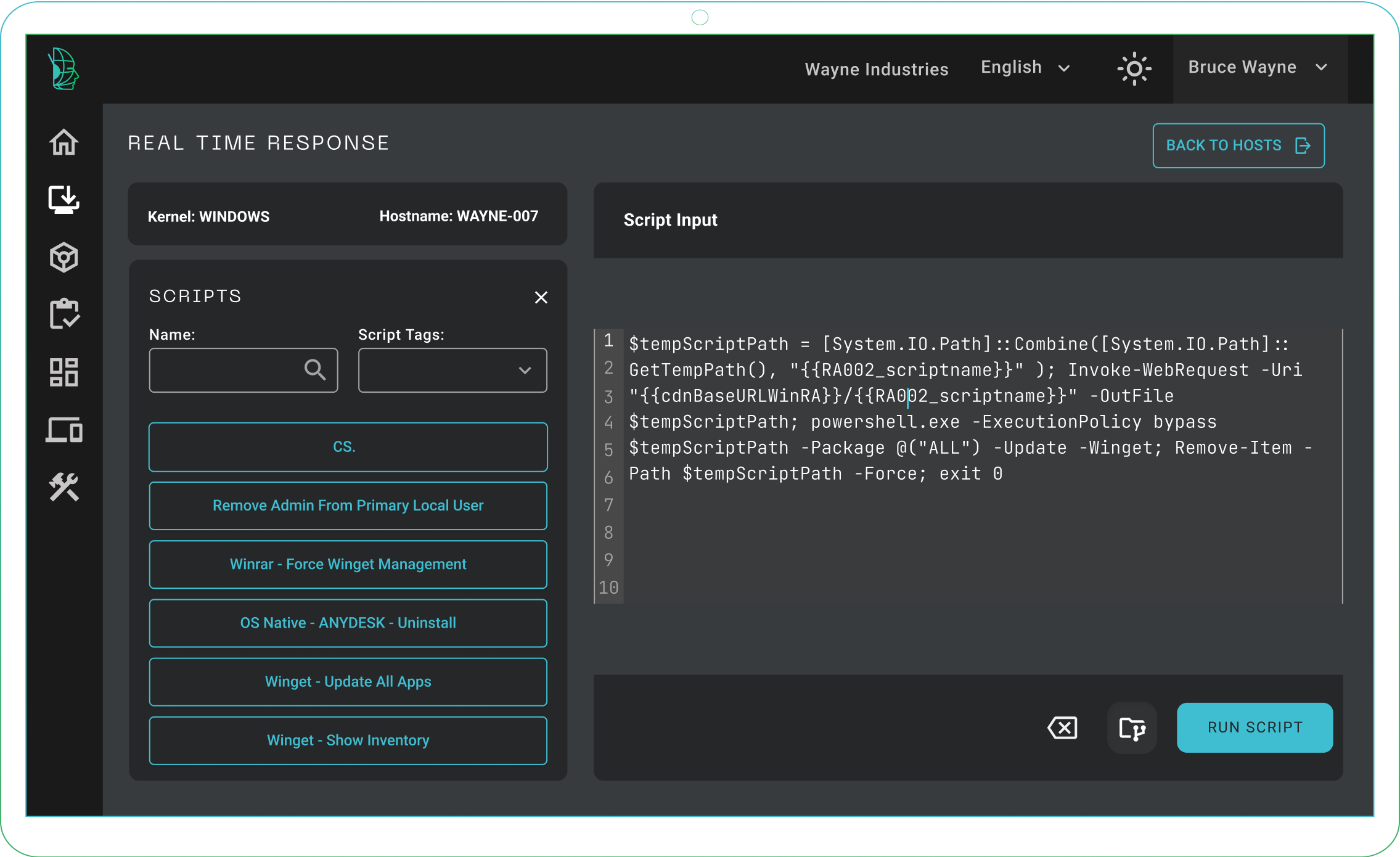
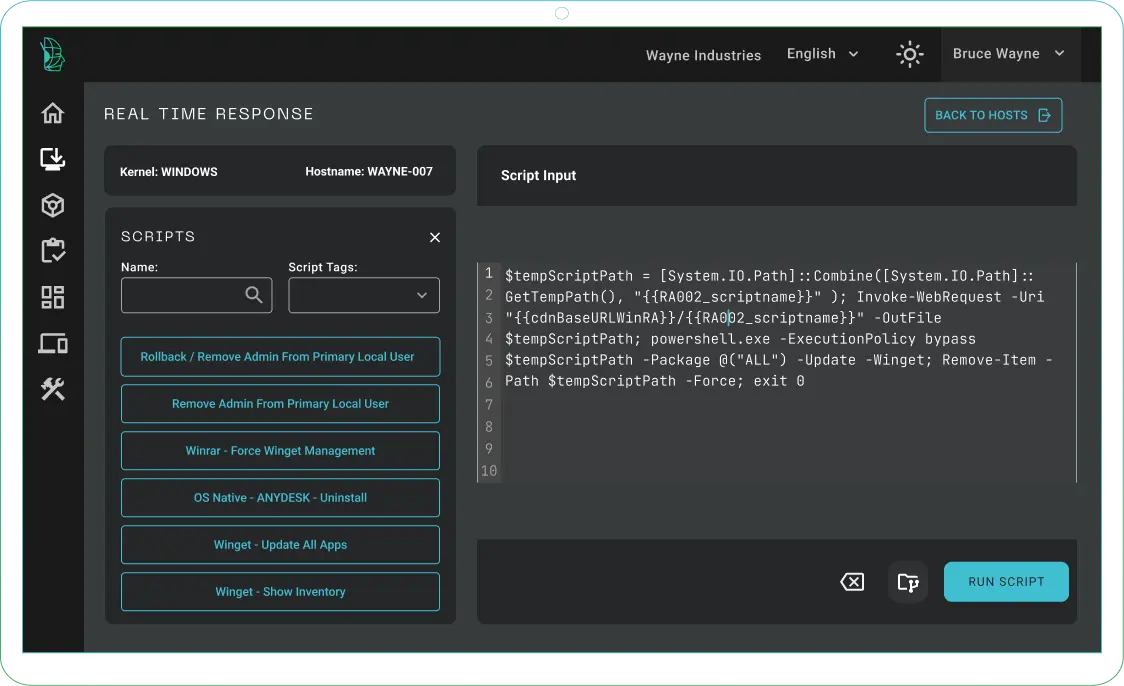
Incident Response
Elevate your cyber defense capabilities
- Scripts automate routine and critical tasks like software updates and security patches across all endpoints.
- Operational efficiency is boosted by reducing manual effort and streamlining processes.
- Simultaneous execution speeds up deployment and remediation across your fleet.
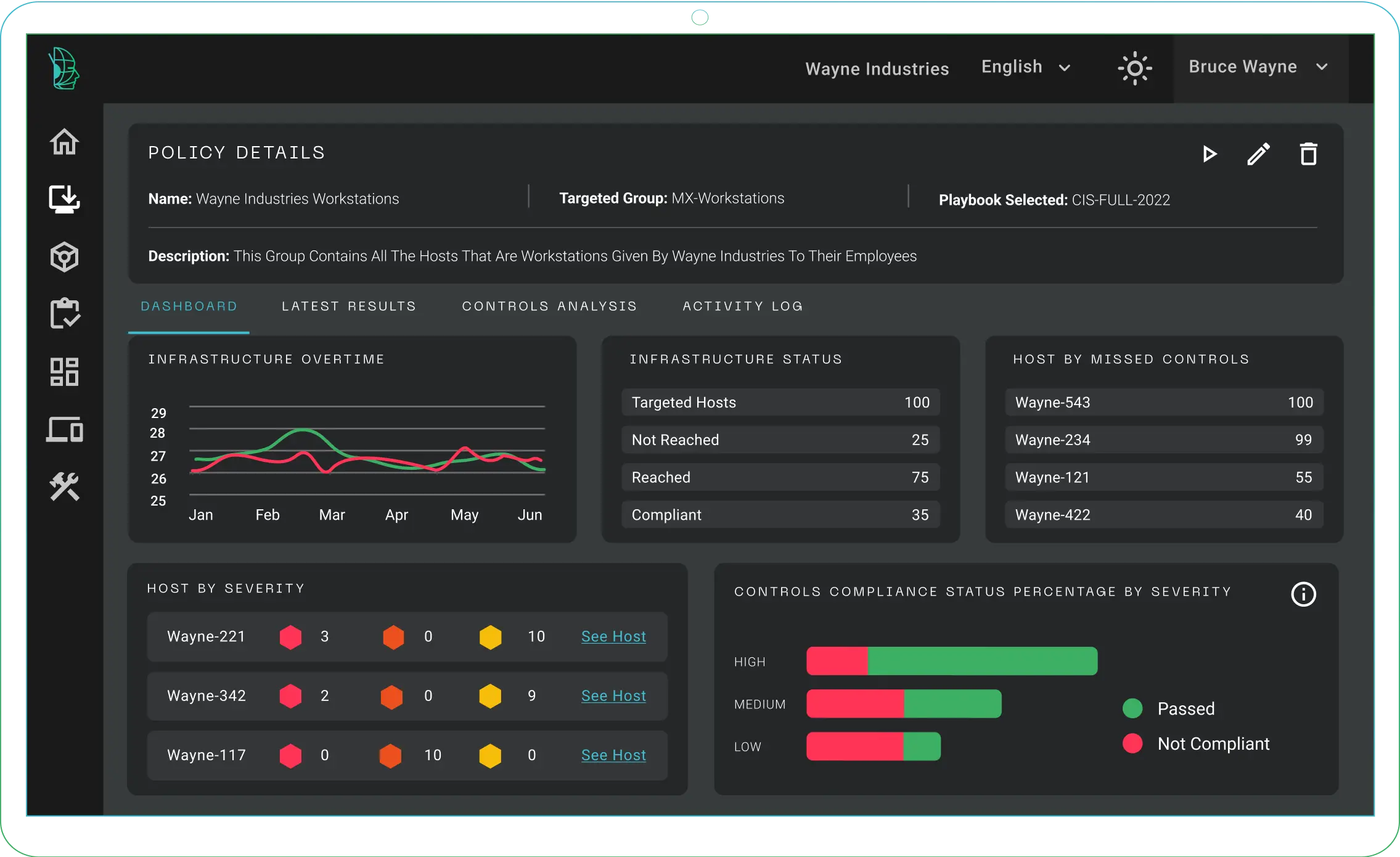
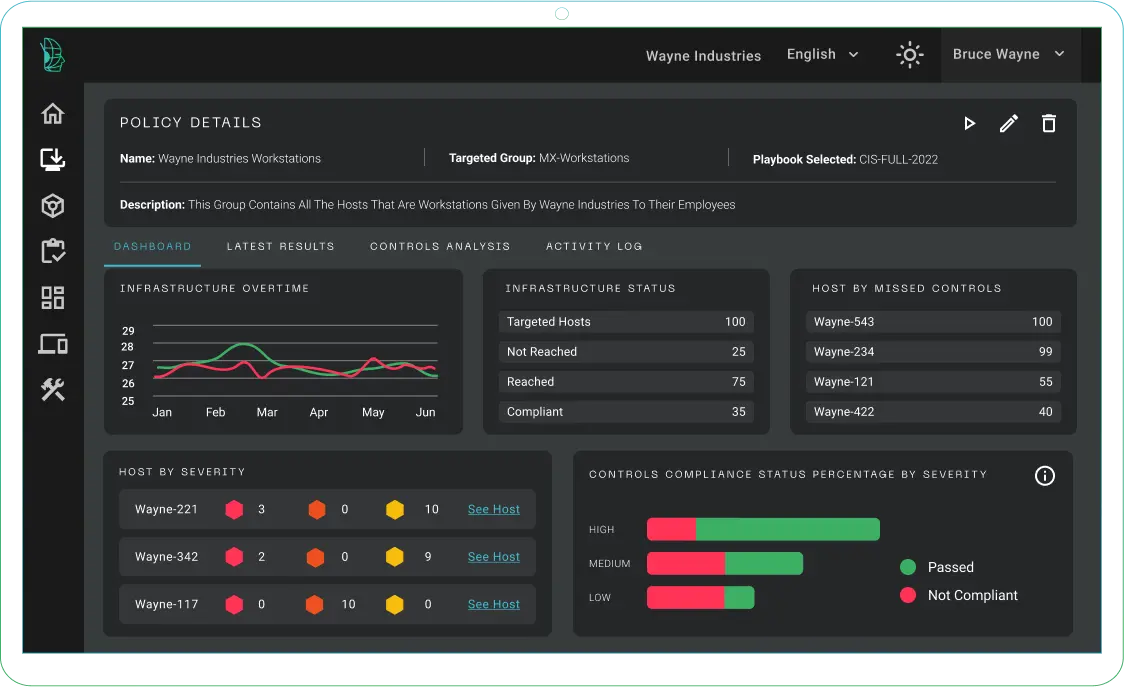
Compliance
Transform compliance into competitive advantage
- Real-time monitoring identifies and corrects deviations.
- Enforces high standards and reduces vulnerabilities.
- Tailored policies that evolve with security needs.
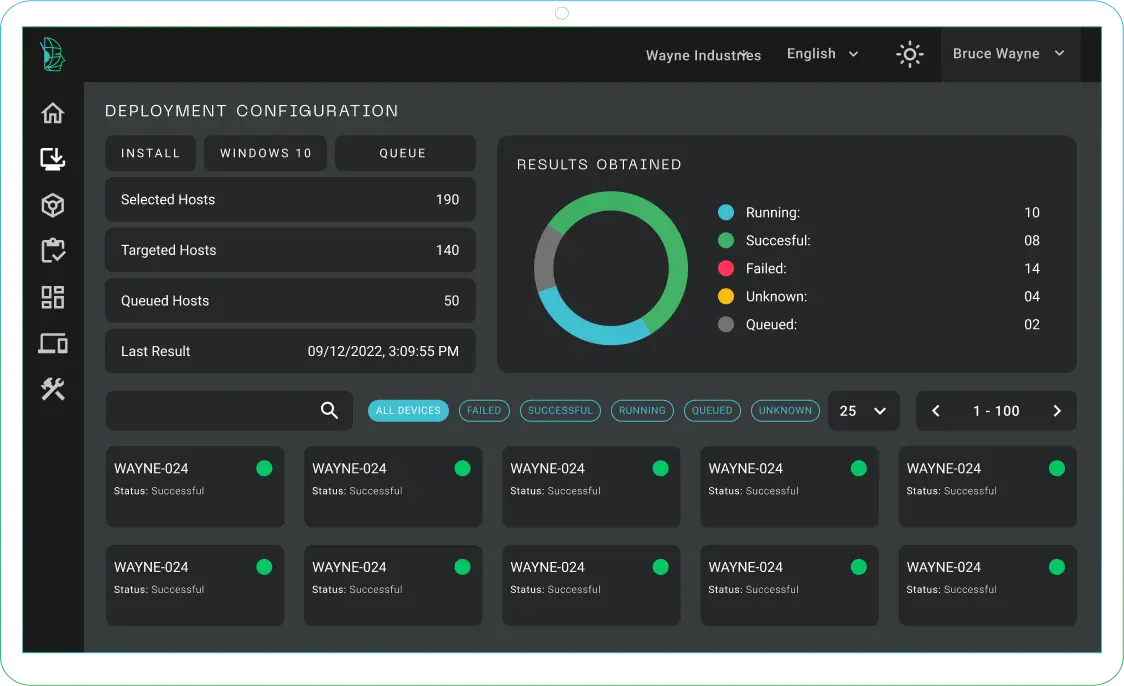
Deploy
Fast-Track your cyber defense operations
- Swift installations for accelerated cybersecurity operations
- Intuitive uninstallation process for effortless system maintenance
- Real-time status checks for reliable implementation
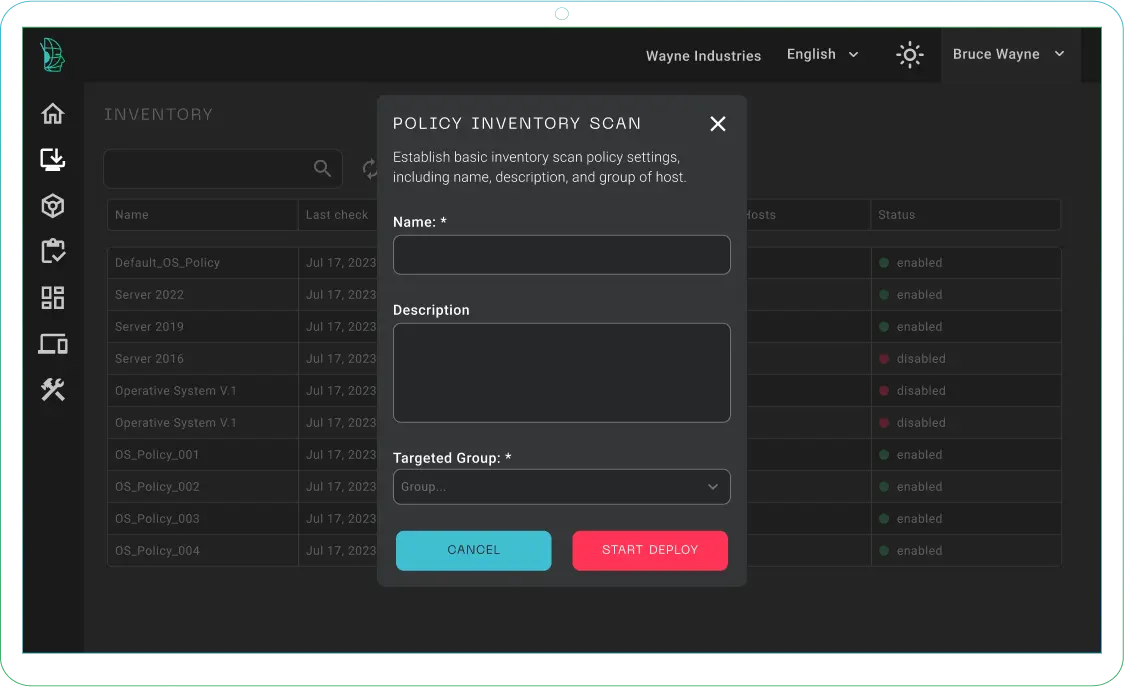
Inventory
Know what you have
- Comprehensive hardware and software inventory for full visibility.
- Efficient asset tracking and management for organized operations.
- Powerful insights for informed decision-making.
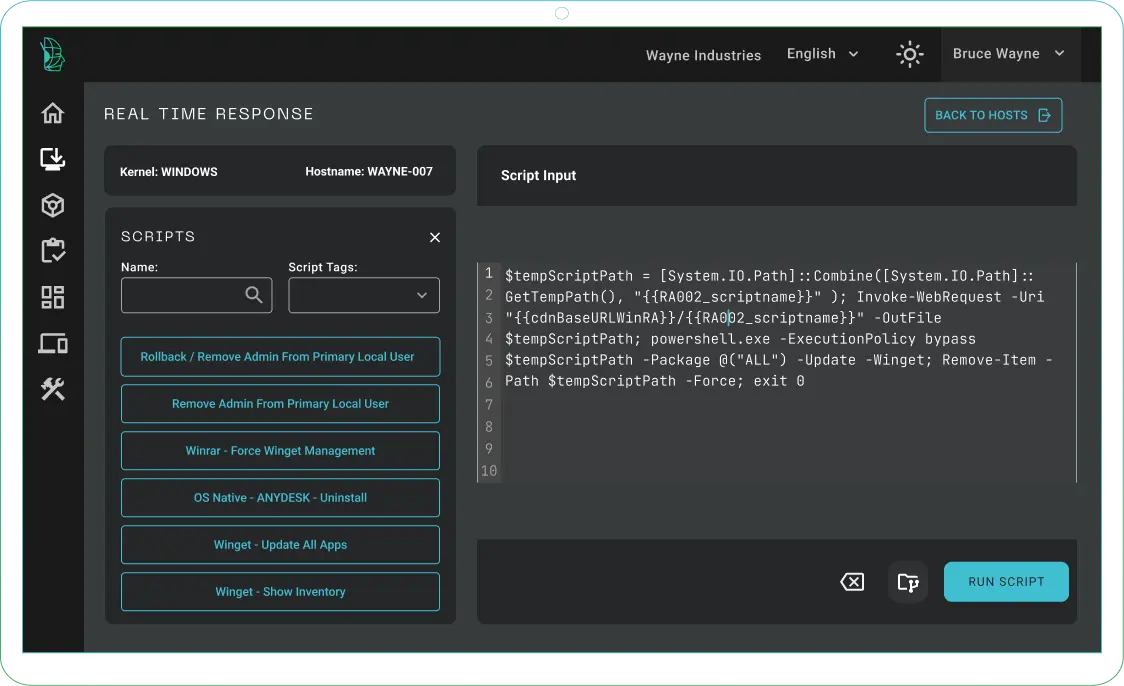
Incident Response
Elevate your cyber defense capabilities
- Scripts automate routine and critical tasks like software updates and security patches across all endpoints.
- Operational efficiency is boosted by reducing manual effort and streamlining processes.
- Simultaneous execution speeds up deployment and remediation across your fleet.
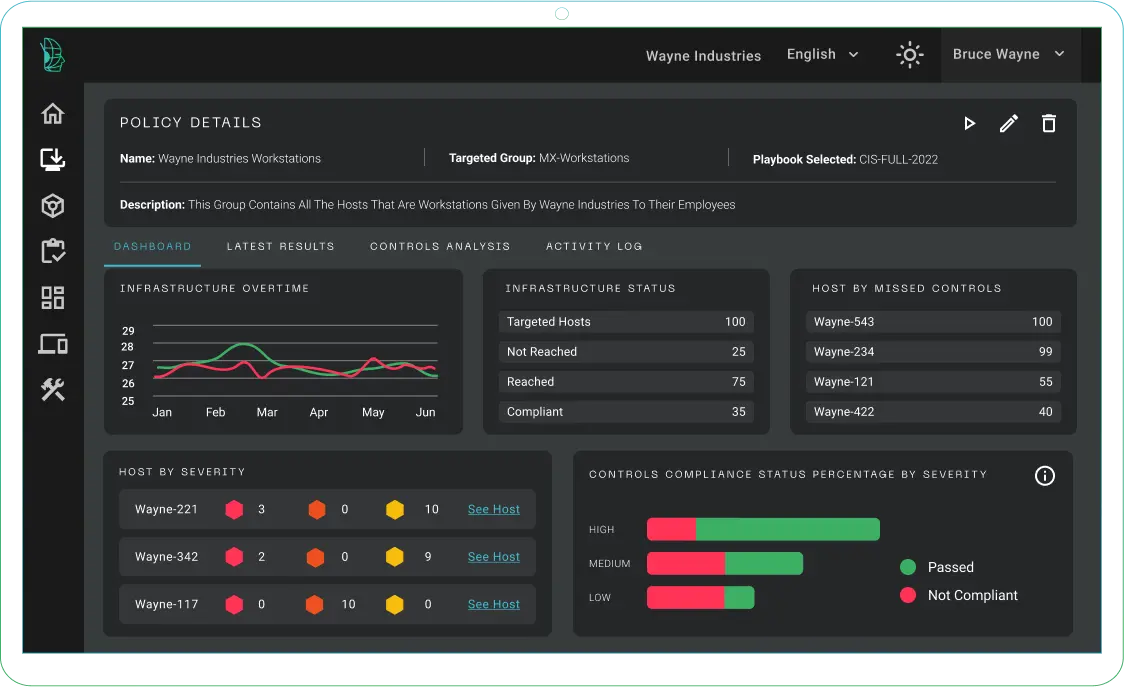
Compliance
Transform compliance into competitive advantage
- Real-time monitoring identifies and corrects deviations.
- Enforces high standards and reduces vulnerabilities.
- Tailored policies that evolve with security needs.
OUR BENEFITS









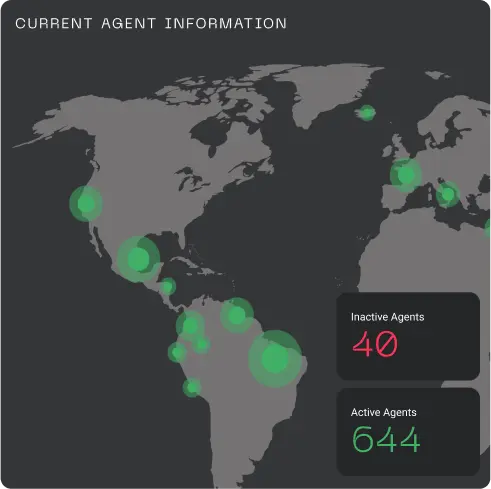

Centralized SecOps Control Plane for Your Fleet
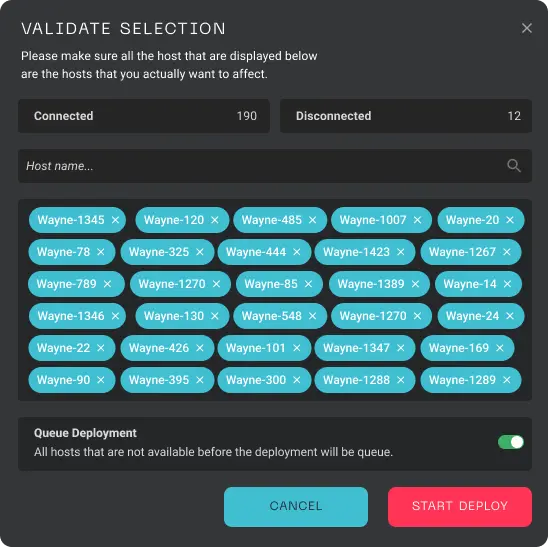
Perform Actions 10x Faster
Improves speed and cybersecurity and IT technology command execution 10 fold which dramatically increases the speed of response to incidents and remediation actions
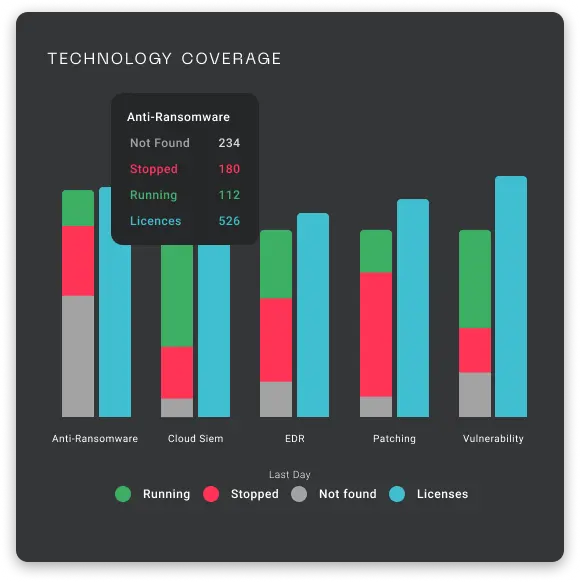
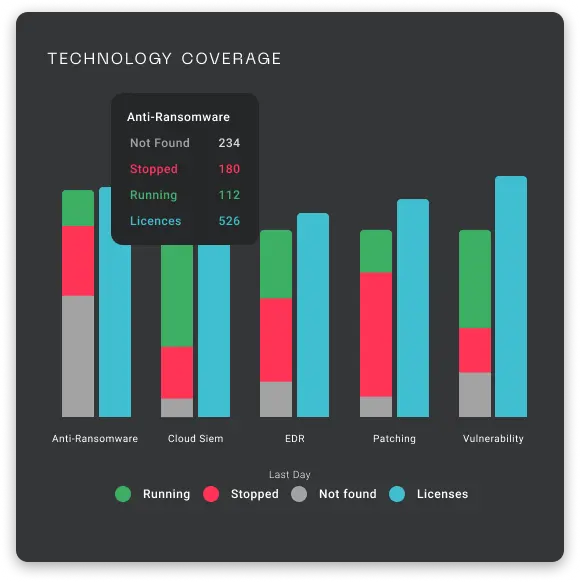
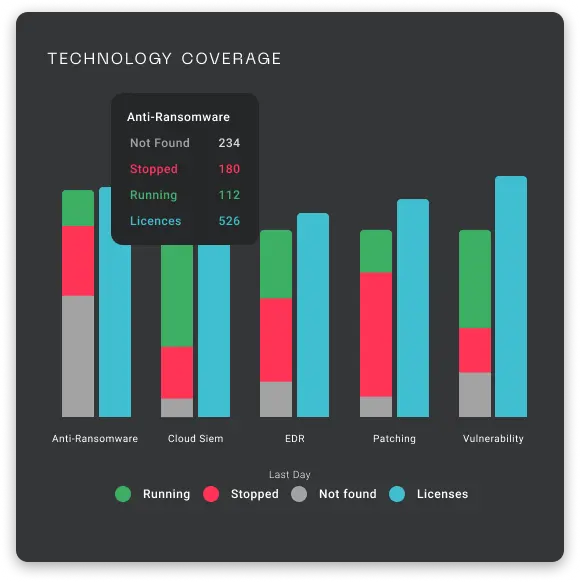
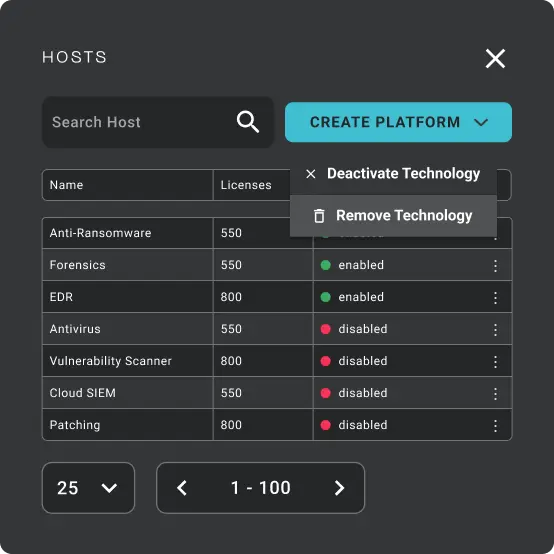
Make use of the technologies and features you're paying for
Verify that current security tools are deployed and working effectively. For example, identifying an endpoint with a disconnected or outdated EDR agent
Best-of-Class with Efficiency of a Platform
Control and freedom to rip and replace endpoint technologies enterprise-wide without complex change management processes
Save Time and Money
Identifies unused software licenses, enabling companies to consolidate technologies and cut costs while enhancing protection
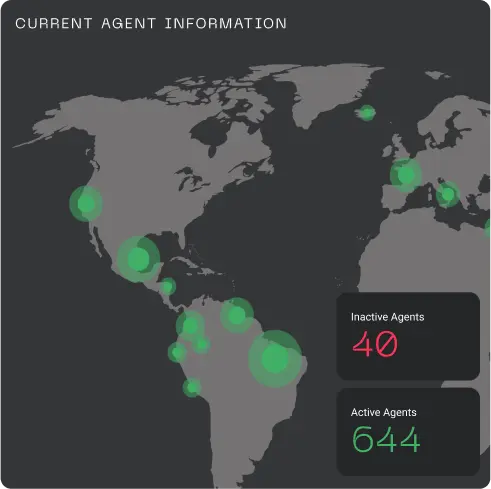
Take Action Across the Entire Fleet
Quickly isolate hosts in the case of a ransomware attack, deploy multiple types of agents in a standardized way, ensure consistency in compliance, and reduce operational overhead and gaps
Perform Actions 10x Faster
Improves speed and cybersecurity and IT technology command execution 10 fold which dramatically increases the speed of response to incidents and remediation actions
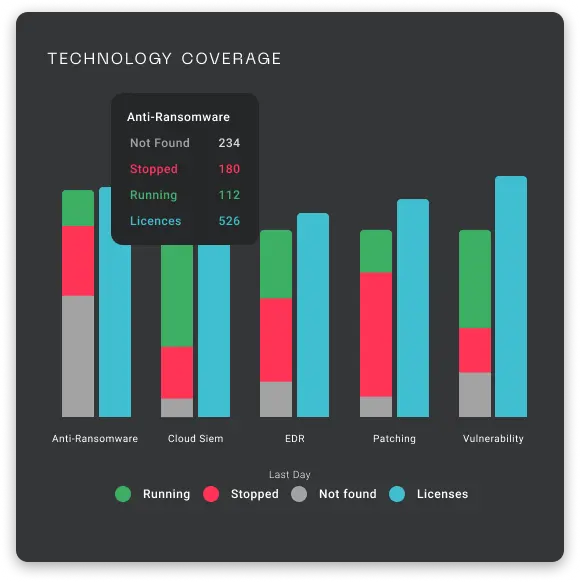
Make use of the technologies and features you're paying for
Verify that current security tools are deployed and working effectively. For example, identifying an endpoint with a disconnected or outdated EDR agent
Best-of-Class with Efficiency of a Platform
Control and freedom to rip and replace endpoint technologies enterprise-wide without complex change management processes
Save Time and Money
Identifies unused software licenses, enabling companies to consolidate technologies and cut costs while enhancing protection
Take Action Across the Entire Fleet
Quickly isolate hosts in the case of a ransomware attack, deploy multiple types of agents in a standardized way, ensure consistency in compliance, and reduce operational overhead and gaps



-
Deploys In Minutes
-
No Extra Management Overhead
-
No Changes to the Existing Infrastructure
-
Fast Time to Value
Don't Just Take Our Word For It
“Metabase Q's Batuta is a game-changer.
Consolidating and updating [subsidiaries with unique operating systems and technologies in] over 30 countries, which used to be lengthy and painful, now takes minutes.”
INDUSTRY VALIDATION
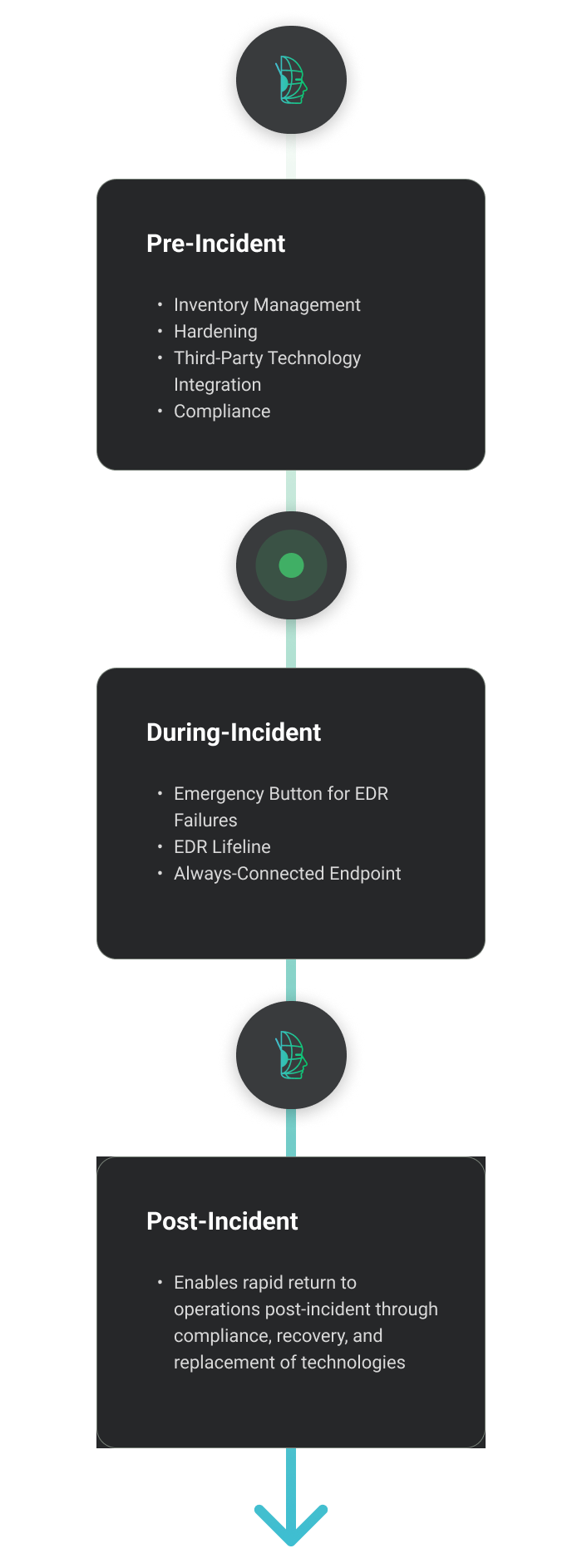
WHY PROACTIVE SECURITY MATTERS

Reduce probability of an attack While increasing 10x the speed of response

Pre-Incident
- Inventory Management
- Hardening
- Third-Party Technology Integration
- Compliance
During-Incident
- Emergency Button for EDR Failures
- EDR Lifeline
- Always-Connected Endpoint
Post-Incident
- Enables rapid return to operations post-incident through compliance, recovery, and replacement of technologies
WHY PROACTIVE SECURITY MATTERS
Reduce probability of an attack while increasing 10x the speed of response
OUR TECHNOLOGY ECOSYSTEM
Reduce Risk and Increase Efficiency With Our Ecosystem of Expanding Integrated Solutions
Get the operational benefit of one platform with integrated best-of-class third-party solutions and the ability to Bring-Your-Own-Technology (BYOT)

Built for Scalability and Complexity
Innovative architecture to simplify complexity and provide a seamless, transparent experience as your business changes

Start Your Path to Proactively Reduce Risk Now
-
No Extra Management Overhead
-
Fast Time to Value
-
No Changes Required to Existing Infrastructure
-
Deploys in Minutes